If you are a defense contractor in Hampton Roads, you have likely heard the acronym CMMC (Cybersecurity Maturity Model Certification) thrown around for years. You may have even treated it like a “someday” problem.
That “someday” has arrived.
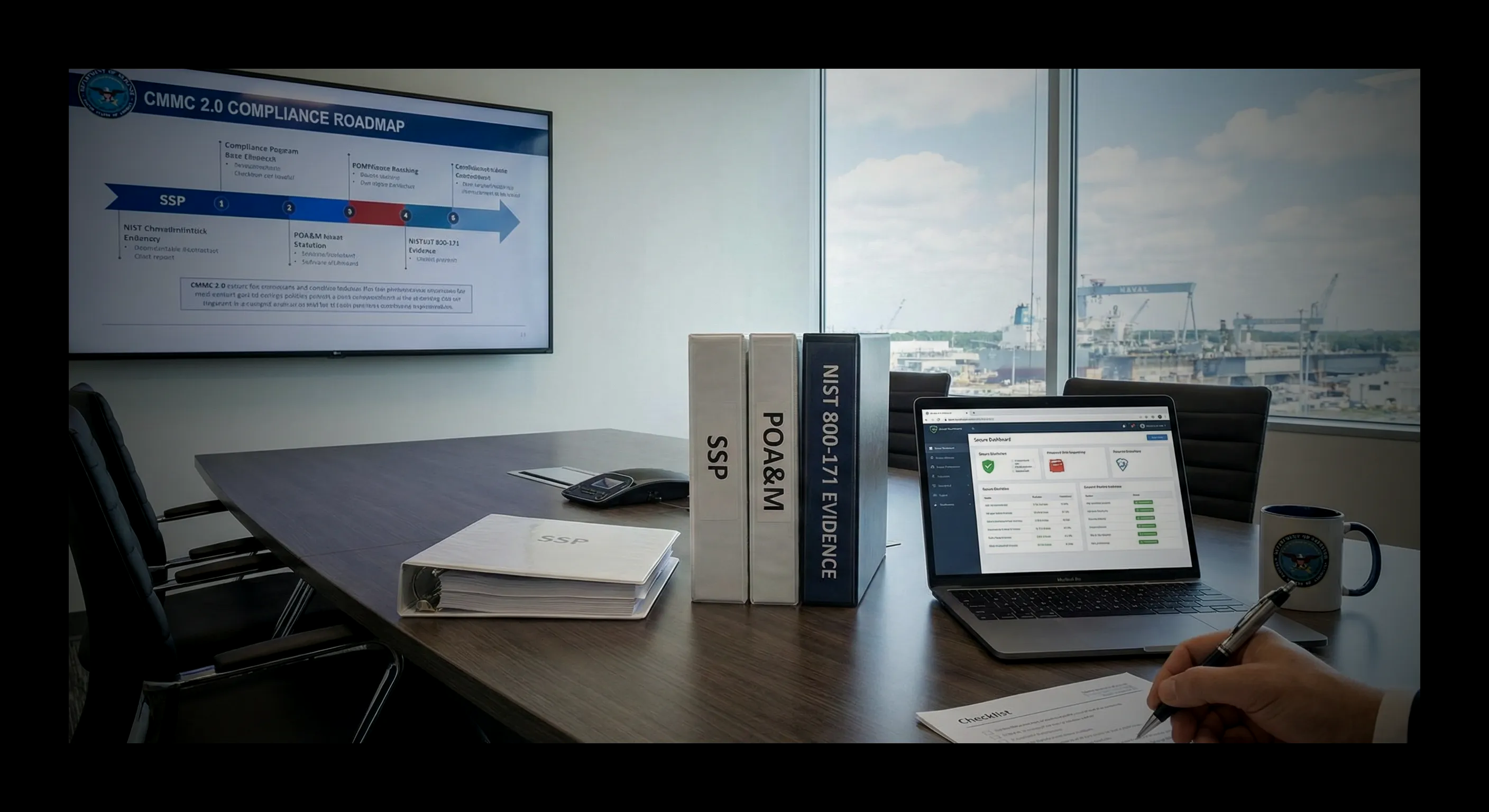
The Department of Defense (DoD) has finalized the rule change. The era of Self-Attestation—where you could simply tell the government you were secure—is ending. Under CMMC 2.0, if you handle CUI (Controlled Unclassified Information), you will be required to pass a 3rd-party assessment (C3PAO) to win or renew contracts.
The “Pass/Fail” Reality
Unlike previous regulations where you could submit a “Plan of Action” (POA&M) for things you hadn’t fixed yet, CMMC 2.0 Level 2 is largely pass/fail.
If you are missing Multi-Factor Authentication (MFA) on a single server, or if your FIPS-validated encryption isn’t configured correctly, you do not get the certification. You do not get the contract.
The NIST 800-171 Breakdown
To pass CMMC Level 2, you must implement the 110 controls defined in NIST SP 800-171. Here is where most local businesses fail during our Gap Analysis:
| Control Family | Common Failure Point |
|---|---|
| Access Control | Allowing employees to share generic logins or passwords. |
| Audit & Accountability | Not retaining server logs for long enough (or at all). |
| Configuration Mgmt | allowing users to install their own software (Shadow IT). |
| Media Protection | Using unencrypted USB drives to move files. |
The Timeline Problem
The biggest mistake we see is contractors waiting until the Request for Proposal (RFP) drops to start their compliance journey.
You cannot implement CMMC overnight.
- Gap Analysis: 2-4 Weeks.
- Remediation (Fixing the gaps): 3-9 Months.
- Audit Prep: 2 Months.
If you start today, you are looking at a 6-12 month runway. If you wait until the contract requires it, you will not have time to certify, and the contract will go to a competitor who prepared early.
How VaBeachTech Helps
We act as your RPO (Registered Practitioner Organization). We don’t issue the certificate (that would be a conflict of interest), but we do everything to get you ready for the auditor.
- We write the SSP (System Security Plan).
- We deploy the SIEM tools to log activity.
- We harden your M365 GCC High environment.
Don’t let a compliance checkmark cost you a multi-million dollar contract.